application Background:
With the development of society, business competition has become increasingly fierce. in order to cope with the market competition, operators have adopted various commercial means or measures such as VIP cards and consumption points. However, how to attract and retain customers and strengthen the management and control of each branch has become a concern for every operator. Membership card management system provides advanced and reliable management means for operators.
II. Design Objective
the use of IC in the safe and effective data with the help of the card as a carrier of safe and effective data POS the machine is powerful and constitutes a simple, convenient and easy to use chain store management system.

Main design objectives.
① safe and convenient IC stored value card sales management, to ensure the security of IC card information.
② achieve flexible sales model to maximize the different needs of customers and improve the competitiveness of enterprises.
③Support multiple communication methods to realize data transmission and exchange, realize statistical analysis, query, printing and other functions
④Improve work efficiency and management level, eliminate duplicate work and save operation cost.
III. Program composition
According to the analysis of business process of chain stores, the system mainly includes card issuance management, daily business processing and data transmission. IC card as electronic money of stored value, all operations are completed independently by the terminal, which completely gets rid of the terminals dependence on the network and has low requirements on network timeliness and sensitivity.
IV. Realization of functions
POS introduction: As embedded products, with the growing popularity of various network-based applications, simple operation, functional and practical, the use of security POS products are widely available in large numbers, according to the use of roughly divided into handheld POS, POS terminals of two kinds.
they all provide users with a common application development platform. Through the preparation of different applications, the different needs of users can easily and flexibly realize the program download and data transmission. At the same time, there are various network connection methods. Users can easily, conveniently, safely and efficiently build application systems for various application IC cards.
①Issuance and management of cards
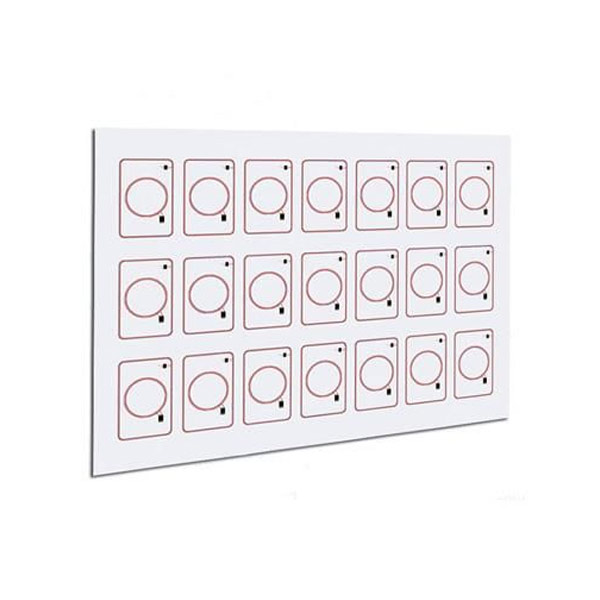
card issuance and management are done at the chain headquarters. First of all, card pre-processing: all cards are written into the enterprise control key in advance, and unified key management is adopted to prevent illegal access and duplication of cards. At the same time, generate administrator cards, terminal operator cards and other operating authority cards for all levels of operating managers. Prevent illegal personnel from accessing the system and operating terminals. Ensure the safe operation of the system.
When issuing user cards (membership cards), the system first verifies the operators authority. After passing, the system generates an access key based on the control key and writes the predetermined amount and other information to the card. the system automatically records card issuance records and operation records.
Finish setting up various functions for POS. Writing applications and loading algorithms.
② Daily business processing
Complete IC sales of stored value cards.
Whether it is door-to-door sales or other sales methods, the business process is roughly the same. Firstly, the verification function is activated and the terminal first verifies the legitimacy of the operator. When the customer presents the membership card for consumption, the terminal will verify the membership card. the verification process is: the terminal reads the user or operator ID access key in the card is generated by a specific algorithm pre-installed in the terminal and compares it with the card key read. the same verification passes.
After normal business processing is completed, the transaction stream is automatically written to the POS as well as to the users membership card. in order to transfer and query the data.
③ Transmission of data
According to the different situations of the chain stores, different network ways of data transmission are selected regularly or irregularly to achieve electronic exchange of various information with the chain stores.
the system provides a variety of connection methods, such as local area networks, public telephone information networks, data collection cards (terminals and when used alone) for data exchange. For example, transaction flow, family information, etc.
Through the management software, it is convenient to summarize and analyze the information and manage the incoming, outgoing, distribution and inventory of distribution centers and chain stores. Effective use of resources. Provide basis for leadership decision. Scientific analysis of consumer demand.
④Expandable functions
According to the actual needs of users, the basic functions of the above system can be easily expanded system functions, very convenient and simple. For example, with the help of IC to realize the electronic management of chain distribution; to realize the function of point of consumption. Only need to modify the POS internal application.
V. Security analysis
the system uses a unified key management to achieve secure management of keys. the key management system uses specific encryption algorithms for encryption to achieve the security of card information. the terminal adopts operation authority management to fully ensure that the terminal is not illegally accessed.
Mutual authentication between the card and the terminal device is direct, without intermediate links. Without dynamic link library authentication of the terminal device, mutual authentication is performed in the form of cipher text within the terminal, and the information is not exposed to ensure the safe operation of the system.
the reading of information in the card requires key verification, and each card has a specific encryption algorithm for reading and writing keys to ensure that the information in the card is not illegally read, and all operations are performed under the control key of the enterprise.