Once upon a time, the access control system gives a symbol of advanced security, but in recent years the news of frequent replication of access cards makes people doubt the security of the access control system. Access card in your hand is still as safe as before?
the security of the access card is determined by two aspects.
First, the encryption program
Cloned access card community in the market friction parking spaces IC part of the manufacturers access control system encryption procedures are relatively simple, most of the access cards currently used in the community is ID encryption IC in general, each set of cards have an independent set of encryption procedures to ensure the independence of each community system. the appearance of access card duplicators on the market indicates that a large number of encryption procedures have been leaked and the security of the community system is beginning to be threatened.
How can you prevent access cards from being compromised in two seconds? the first thing to do is not to lend your access card to anyone else. in addition, security insiders suggest that communities can regularly refresh or replace the serial number of the access card and take encryption measures IC card, change the code, the previous automatically invalid.
Software and hardware generally use distributed systems, which allows the security of the entire system to assume multiple subsystems, assuming local failure, does not affect the operation of the entire system, machine installation of online virus firewall, database recovery capability after failure, system password, program, file, database authorization protection; IC physical and logical encryption card data, to achieve a card a secret.
Develop a strict management process for IC; when issuing the key, the system uses the one-card-one-secret algorithm to calculate the system password, which is the only key that customers and equipment suppliers cannot crack, with absolute security.

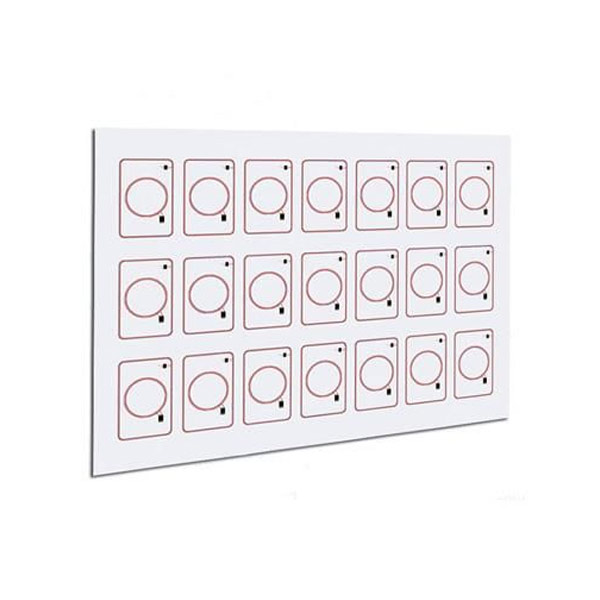
Second, the choice of access control card
1. Each sector in the card has two sets of passwords (KEY_A, KEY_B) each fan area password and access control is independent; the card also has encryption logic and communication logic circuit. IC card will first verify the triple password each time the card is read, and then read the other information on the card.
2. card and read-write exchange data when data.56Mhz RF signal, not easy to intercept, even if illegal interception, can not access the data in the card, because there is no read-write password.
3. in the system application, the use of a card a secret encryption mechanism and machine dynamic generation access password, to prevent the card was deciphered, and other companies together with IC actually card only used IC card physical card number has the essential difference, also has the fundamental reason to distinguish IC card was cracked;.
4. the use of DES algorithm to encrypt data packets.
5. the use of effective card key management mechanism to effectively eliminate counterfeit cards.
6. Each application system of the system uses a fan area designated by the customer with a different password. in addition to the system equipment can access the two public information fan area, the data on each business application subsystem can not be read or written by other subsystems; According to the different identities of cardholders, the card is classified and managed, and different privileges and functions are granted to
Talk about how to encrypt the access control card and the security performance of the access control card
improve security.
7. Each card has a unique serial number, which needs to be registered and issued before using the system. Each issued card IC card registration number, elevator access control privileges and other permissions downloaded in advance to the system machine registration form and permission table.
therefore, we can conclude that only the perfect combination of encryption programs and access control cards to create a secure access control system.