As electronic identification replaces the need for face-to-face and paper, the need for security and enhanced privacy is increasing. the emergence of a global internet that includes customers and suppliers and the expansion of enterprise networks has accelerated the demand for solutions based on public key cryptography.
Smart Cards
A few examples of the various services enabled by public key cryptography are secure channel communications over public networks, digital signatures to ensure image integrity and confidentiality, client-to-server authentication (and vice versa), and strongly authenticated Smart cards.

the Microsoft Windows operating system platform is the best and most cost effective computing platform for developing and deploying Smart card solutions.
What is a Smart card?
A Smart card is a tamper-proof minicomputer. the Smart card itself contains the CPU and some non-volatile storage. in most cards, some of the memory is tamper-proof and the rest can be accessed by any application that can talk to the card. This feature allows the card to retain some secrets, such as the private key associated with any certificate it holds. the card itself actually performs its own encryption operations.
While Smart cards are often compared to hard drives, they are "secure drives with brains" - they store and process information. to communicate with a reader or coupler, Smart cards are a storage device with a core mechanism. they have a file system configuration and can be divided into available or locked public and private space. there are also isolated areas for protecting information, such as certificates, e-wallets and entire operating systems. in addition to traditional data storage states such as read-only and read/write, some vendors are using sub-states that best describe "add-only" and "update only".
Currently, Smart cards come in two forms: contact and contactless.
Card readers require a card reader to facilitate a two-way connection. the card must be inserted into a contact point device on the touch card, which helps communicate with the card chip. As with todays desktop CPUs, contact cards use 3-volt and 5-volt models. Contact card readers are typically built into a serial or universal serial bus that connects to computer desktop (USB) company or vendor owned buildings and assets, cell phones, handheld devices, stand-alone devices, ports, laptop slots and keyboards.
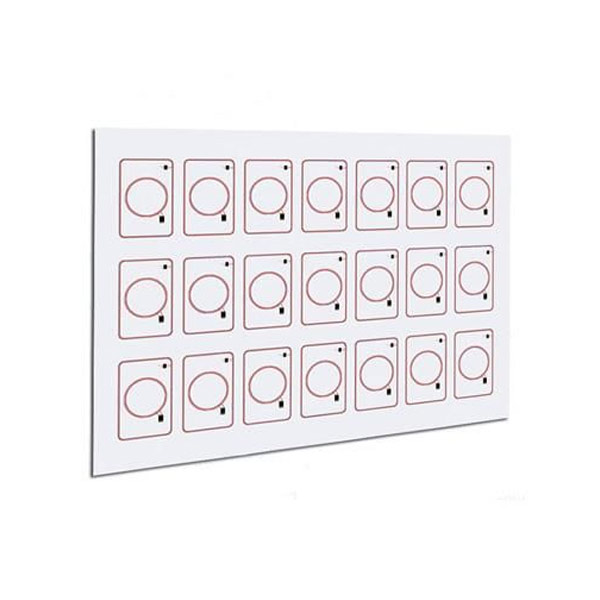
Contactless cards use proximity couplers to obtain information from and from the card chip. As the card radiates from the coupler to a specific distance, the antenna wraps around the circumference of the card and is activated. the cards antenna and coupler are configured to facilitate connection states from a few centimeters to a few feet. By using a combination of the card manufacturers hard-coded chip algorithms, the two-way transmission is encoded and encrypted; a randomly generated session number; and a cardholder certificate, secret key, or personal identification number (Pin). in the coupler range, the complexity of the connection can facilitate separate and discrete connections for multiple cards. Since contactless cards do not require physical contact with the reader, the range of usability is greatly expanded.